Automated Threat Protection
Elastic Security for automated threat protection
Thwart complex attacks with machine learning and behavior analytics. Block ransomware and malware from any infrastructure. Advance SecOps maturity to stop threats at scale.
Validated by security experts
Security teams worldwide automate threat protection with Elastic Security.
Customer spotlight
Oak Ridge National Labs safeguards some of the world’s fastest computers with Elastic machine learning.
Customer spotlight
Using detection rules aligned with MITRE ATT&CK®, Elastic secures a major university.
Customer spotlight

Martin's Point Health Care protects hosts with unified endpoint security from Elastic.
Foil attacks with automated threat protection
Prevent and detect cloud-based or on-premise threats with centralized and agent-based protections aligned with MITRE ATT&CK.
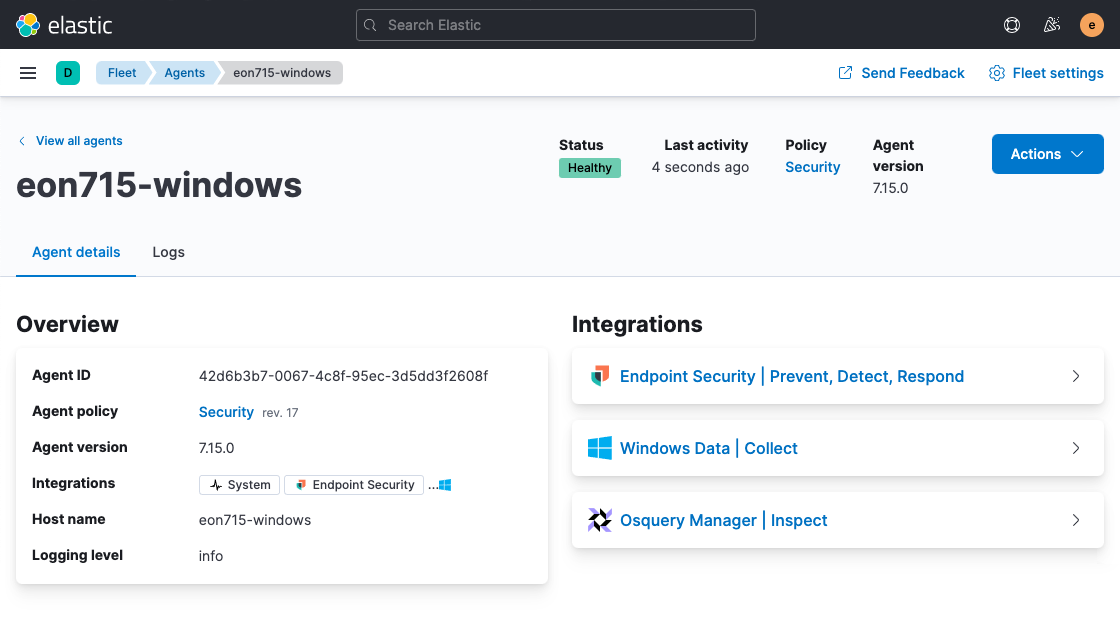
Prevent, detect, and respond with a single agent
Prevent and detect threats with Elastic Agent, harnessing the specialized expertise of Elastic Security Labs. Disrupt complex attacks with malicious behavior protection — pairing advanced analytics and tailored response actions. Automatically erase attack artifacts from infected systems. Block fast-evolving ransomware and malware.
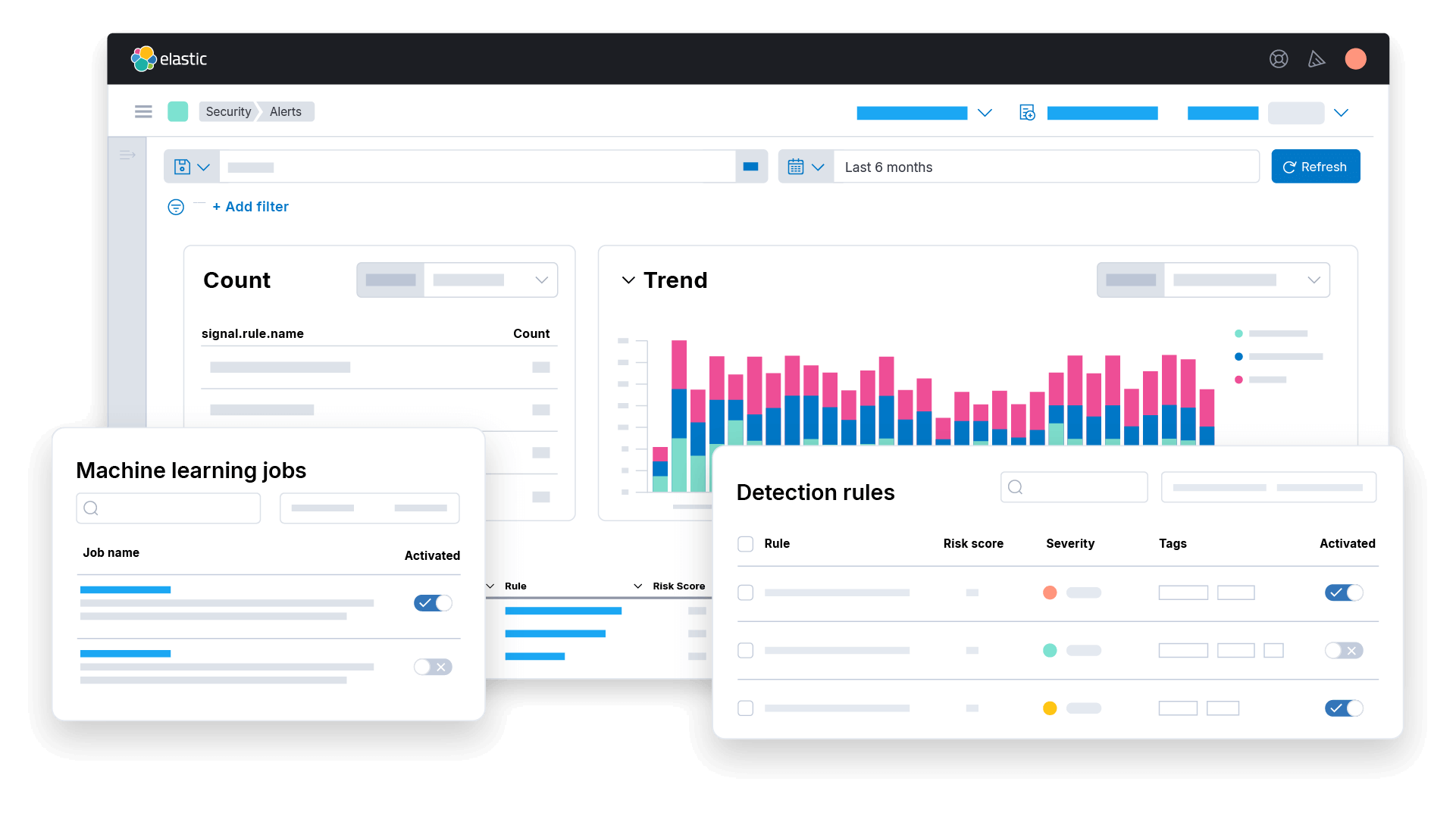
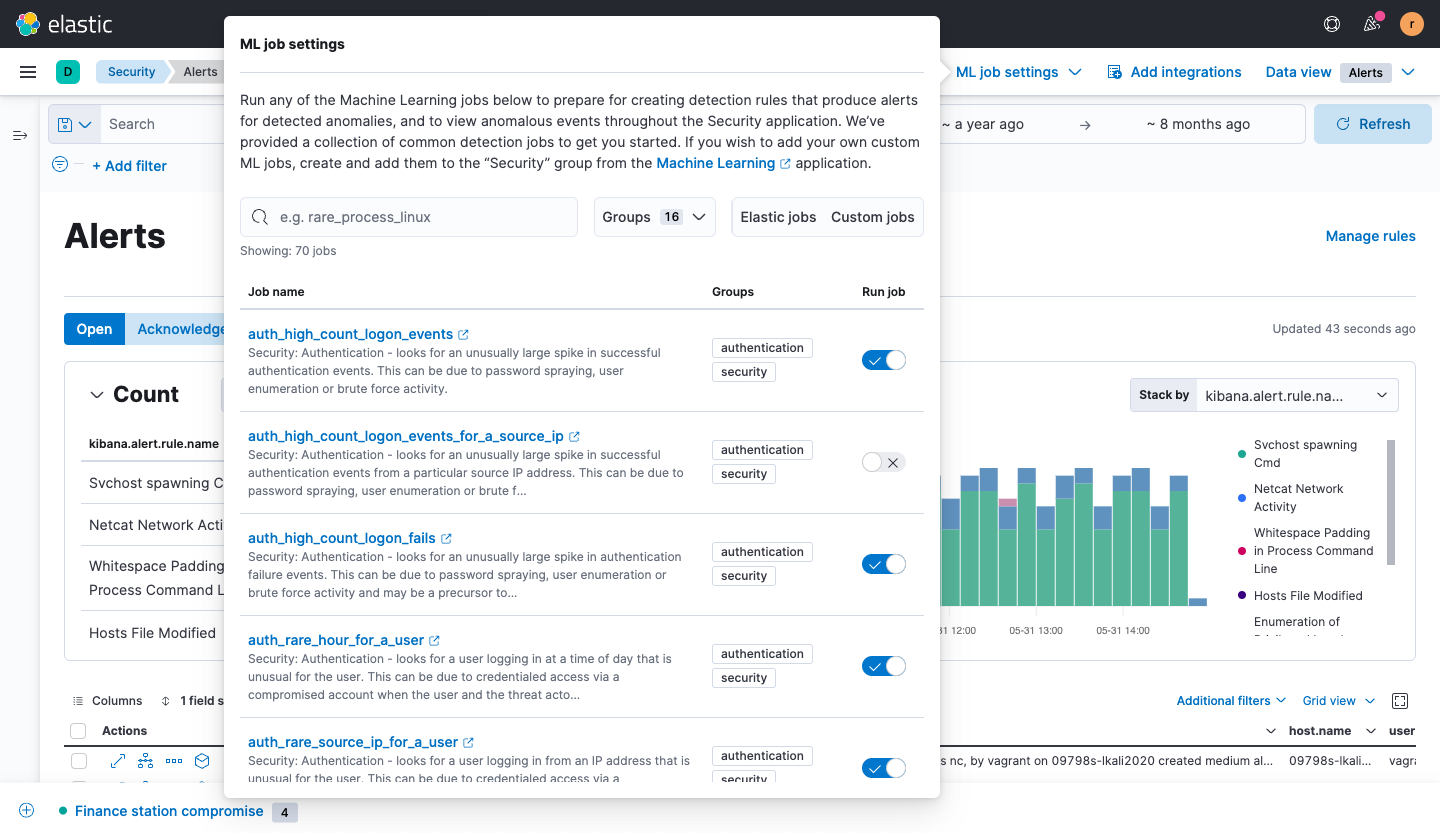
Uncover hidden threats with advanced security analytics
Spot suspicious behavior with machine learning across diverse data sources. Expose adversarial activity often missed by traditional detection methods, including malicious insiders and advanced persistent threats. Apply turnkey machine learning jobs to advance protection rapidly.
Detect known threats with alerting
Reveal threats early in the attack lifecycle (before damage is done) with rules honed and shared by Elastic threat researchers and community members. Automatically enrich and corroborate alerts to prioritize the most critical attacks. Leverage threat intelligence for further fidelity.
Do more with Elastic
Bring the speed, scale, relevance, and simplicity of Elastic to teams of all types.
Security
Prevent, detect, and respond to threats — quickly and at scale.
Observability
Analyze logs, metrics, and APM traces in a single stack.
Enterprise Search
Power search experiences for your workplace, website, or apps.

















